

is your proposal inspired by Biden administration forgives $4.5 billion in student debt for over 60,000 public service workers ?
cultural reviewer and dabbler in stylistic premonitions


is your proposal inspired by Biden administration forgives $4.5 billion in student debt for over 60,000 public service workers ?


The headline should mention that they’re breaking 22-bit RSA, but then it would get a lot less clicks.
A different group of Chinese researchers set what I think is the current record when they factored a 48-bit number with a quantum computer two years ago: https://arxiv.org/abs/2212.12372
I guess the news here is that now they’ve reached 22 bits using the quantum annealing technique which works on D-Wave’s commercially-available quantum computers? That approach was previously able to factor an 18-bit number in 2018.
🥂 to the researchers, but 👎 to the clickbait headline writers. This is still nowhere near being a CRQC (cryptanalytically-relevant quantum computer).
this is probably a stronger argument to get people to vote for her:
 what she’ll do
what she’ll do
 what her opponent won’t be able to do if she wins.
what her opponent won’t be able to do if she wins.
there are more photos here: https://commons.wikimedia.org/wiki/Category:Crown_shyness


headline was more exciting before i read the last four words of it


i can’t help but wonder if there isn’t some more useful science that these scientists could be doing (i write, while reading garbage on the internet)


All two-letter TLDs are ccTLDs.
However, several of them are not in ISO 3166-1.


I don’t think any of his stuff would seem shocking by today’s standards.


Or you could just… learn to use the modern internet that 60% of internet traffic uses? Not everyone has a dedicated IPv4 anymore, we are in the days of mobile networks and CGNAT. IPv4 exhaustion is here today.
Where are you getting 60%? Google’s IPv6 Adoption page has it under 50% still:
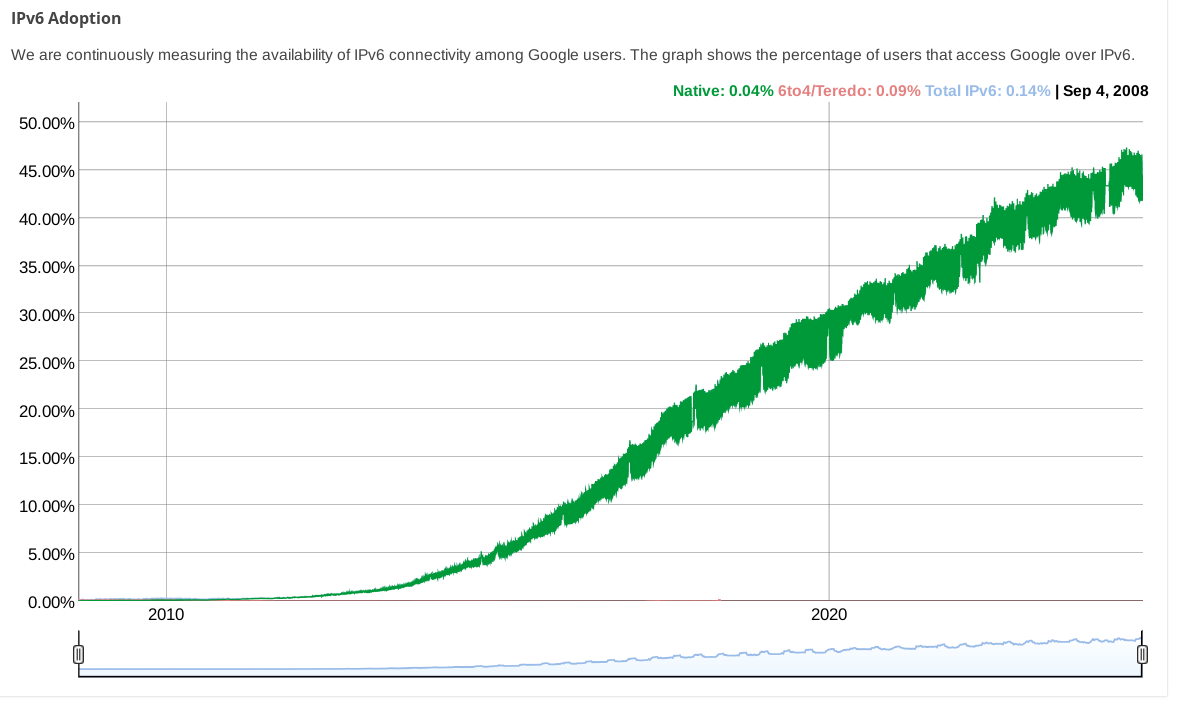
(while other stats pages from big CDNs show even less)


Sounds good, until looking closer and finding out: “For an initial period of 99 years, the United Kingdom will be authorised to exercise with respect to Diego Garcia the sovereign rights and authorities of Mauritius required to ensure the continued operation of the base well into the next century” 😦


If you have ::/0 in your AllowedIPs and v6 connections are bypassing your VPN, that is strange.
What does ip route get 2a00:1450:400f:801::200e (an IPv6 address for google) say?
I haven’t used wireguard with NetworkManager, but using wg-quick it certainly adds a default v6 route when you have ::/0 in AllowedIPs.


You could edit your configuration to change the wireguard connection’s AllowedIPs from 0.0.0.0/0 to 0.0.0.0/0,::/0 so that IPv6 traffic is routed over it. Regardless of if your wireguard endpoint actually supports it, this will at least stop IPv6 traffic from leaking.


ipv4 with an extra octet
that was proposed as “IPv4.1” on April 1, 2011: https://web.archive.org/web/20110404094446/http://packetlife.net/blog/2011/apr/1/alternative-ipv6-works/


The article text doesn’t support the headline (“Biden helped end the dockers strike by saying reopening the ports to help Hurricane Helene victims would be patriotic”):
“ With the grace of God, and the goodwill of neighbors, it’s gonna hold,” President Joe Biden told reporters Thursday night after the agreement.
In a statement later, Biden applauded both sides “for acting patriotically to reopen our ports and ensure the availability of critical supplies for Hurricane Helene recovery and rebuilding.”
[…]
Thursday’s deal came after Biden administration officials met with foreign-owned shipping companies before dawn on Zoom, according to a person briefed on the day’s events who asked not to be identified because the talks were private. The White House wanted to increase pressure to settle, emphasizing the responsibility to reopen the ports to help with recovery from Hurricane Helene, the person said.
Acting Labor Secretary Julie Su told them she could get the union to the bargaining table to extend the contract if the carriers made a higher wage offer. Chief of Staff Jeff Zients told the carriers they had to make an offer by the end of the day so a manmade strike wouldn’t worsen a natural disaster, the person said.
By midday the Maritime Alliance members agreed to a large increase, bringing about the agreement, according to the person.
In some places it is:



would this text land differently if “public school” were replaced with “school”? 🤔
Marmite was first